Without regular audits, encryption often remains error-prone and insecure. Vulnerabilities such as outdated algorithms, insecure key management, or faulty configurations jeopardize sensitive data and incur high costs due to data breaches. An audit uncovers these issues and ensures the use of modern encryption methods like AES-256 and TLS 1.3.
Important facts:
- Average cost of a data breach: $4.45 million (2024)
- Common vulnerabilities: Insecure keys, outdated algorithms, non-compliance with GDPR
- Audits check compliance, key rotation, and technical configurations
- Costs for external audits: €5,000–25,000
Benefits for platforms like Gunfinder:
- Protection of sensitive data (e.g., payment information)
- Compliance with legal requirements (e.g., GDPR, PCI DSS)
- Strengthening user trust through verified security measures
Audits are essential for identifying security gaps and keeping encryption systems up to date. They provide clear measures for improvement and ensure the protection of sensitive data.
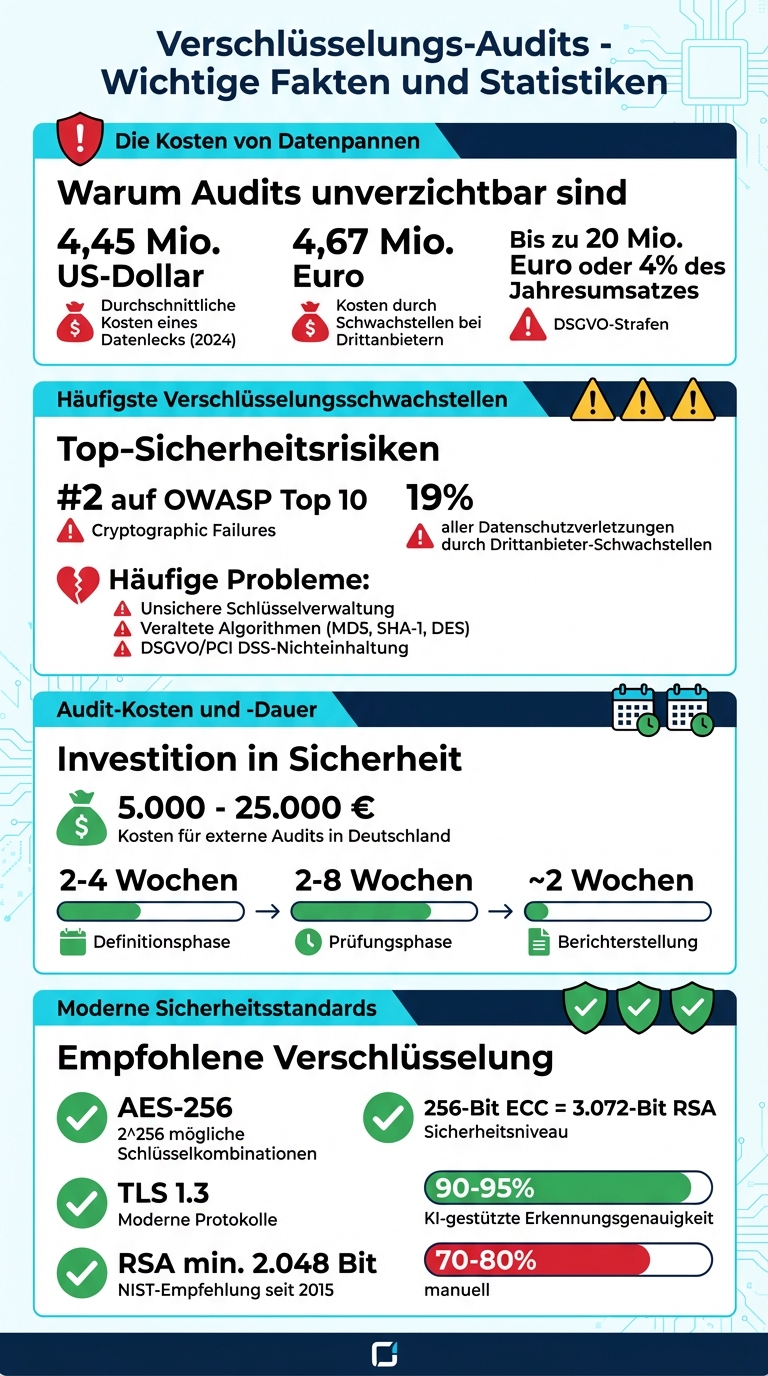
Encryption Audits: Costs, Vulnerabilities, and Security Statistics at a Glance
Security Audit Basics: Tips for Effective Governance and Risk Management
sbb-itb-1cfd233
Common Encryption Vulnerabilities and Their Risks
Encryption systems can fail in many ways – and each vulnerability provides attackers with the opportunity to access sensitive data. The OWASP Top 10 lists “Cryptographic Failures” as the second greatest security risk [5]. Particularly alarming is that these problems often do not arise from a lack of encryption, but from faulty implementation.
Poor Key Management
Even the strongest encryption is useless if the keys are managed insecurely. Common mistakes include:
- Hardcoded keys in source code (CWE-321)
- Missing key rotation
- Unsecure management, e.g. in Excel spreadsheets [5][6]
Manual procedures for key management are not only error-prone but also insecure. Once a key is compromised, attackers can decrypt all data protected by it. This is particularly critical for payment information or personal data. Since 2015, NIST has recommended at least 2,048 bits for RSA keys, as 1,024-bit keys are considered insecure and can be cracked by state actors [1][6].
Outdated encryption algorithms
The use of outdated algorithms also poses significant risks. Examples like MD5, SHA-1, or DES have known vulnerabilities (CWE-327) [5]. MD5 and SHA-1 are susceptible to hash collisions – a problem that attackers can exploit to forge digital signatures [7]. Similarly, older protocols like SSLv3 or TLS 1.0 are vulnerable to attacks such as POODLE or BEAST [7].
Modern standards like AES-256, on the other hand, offer practically unbreakable security against brute-force attacks due to 2^256 possible key combinations [1]. Chester Avey from GlobalSign emphasizes:
“Switching to more robust hash functions like SHA-3 significantly increases the complexity needed to compromise systems protected by cryptographic hashing" [7].
Non-compliance with regulatory requirements
Violations of regulations such as GDPR or PCI DSS can result in hefty fines and a significant loss of trust [5]. These regulations explicitly require the use of strong encryption, especially for personal data and payment information. Typical violations include:
- Unencrypted data transmission over HTTP or FTP (CWE-319)
- Weak password hashes without salt (CWE-759)
- Low entropy in key generation (CWE-331) [5]
Without regular audits, such vulnerabilities often remain undetected – until a security incident occurs.
These examples demonstrate how important it is to regularly review and update encryption systems to close security gaps and protect data integrity.
How regular audits improve encryption security
Regular audits turn theoretical security concepts into concrete protective measures. They uncover vulnerabilities such as Shadow IT (unauthorized IT applications), uncontrolled end devices, and unencrypted backups – aspects that can easily be overlooked in everyday operations [8][2]. Especially in cloud environments, the Shared Responsibility Model is examined. This ensures that companies manage their keys and configurations correctly, rather than blindly relying on the provider [8][9]. The following explains how audits detect and address these security gaps.
Detecting encryption gaps
An audit often begins with a vulnerability analysis, where all active services are recorded and compared with known vulnerabilities from CVE databases [2]. Automated tools and expert analyses identify vulnerabilities in firewalls and policies and document them in detailed reports [11]. Additionally, Computer Assisted Auditing Techniques (CAAT) and monitoring software such as Nagios or Tripwire are used. These tools monitor configuration changes in real-time and help ensure continuous encryption security [2].
Check Strong Encryption Protocols
Auditors check whether recommended algorithms such as AES-256 or TLS 1.3 are used and identify insecure methods such as RSA-1024 or DES [8][1]. For example, a 256-bit ECC key (Elliptic Curve Cryptography) provides the same level of security as a 3,072-bit RSA key but is significantly more efficient [1]. With the NIS-2 Directive, which has been in effect in the EU since January 2023, the requirements for regular security audits and risk assessments have further increased [2].
Check Independent Key Control
A central point in key management is segregation of duties – no one should control the entire lifecycle of a cryptographic key alone [8]. Gary Glover from SecurityMetrics puts it succinctly:
“If you don’t protect the location of the encryption key... it’s like leaving your house key in the door lock" [14].
Auditors conduct sampling tests to ensure that keys can be securely retrieved, rotated, and deleted [10][8]. In AWS systems, they check specific permissions such as kms:Describe* to ensure that key configurations can be examined without compromising the keys themselves [10]. Compliance is verified by matching policies with technical evidence such as rotation and deletion logs [8].
The Audit Process in Detail
This section explains step by step how an encryption audit is conducted to comprehensively review security measures.
Such an audit covers legal, technical, and organizational aspects. Within 2–4 weeks, the audit framework is defined and key stakeholders are identified. The actual audit lasts 2–8 weeks, followed by about 2 weeks for report preparation. In Germany, the costs for external audits vary between €5,000 and €25,000 depending on the size of the company [16].
Examination of Regulatory Compliance
The first step is to verify whether the technical and organizational measures (TOMs) have been implemented in accordance with Article 32 of the GDPR. Auditors check the record of processing activities (Art. 30 GDPR) for currency and verify whether documented encryption measures have actually been implemented. Contracts with processors (Art. 28) are also reviewed. Additionally, it is ensured that international standards such as ISO 27001:2022 Annex A 8.24 are adhered to, which regulates the use of cryptography. Konstanze Krollpfeiffer, certified data protection officer, puts it succinctly:
“A data protection audit is a systematic process in which the current level of data protection of a company is examined, evaluated, and documented" [16].
This step goes beyond mere compliance and strengthens the trust of Gunfinder users.
Technical Tests and Code Analysis
In the next phase, penetration testing methods such as OWASP, OSSTMM, and PTES are used to simulate potential cyber attacks. Tools like Nessus search for known vulnerabilities, while Metasploit tests whether encryptions can be bypassed. Network analysis tools like Nmap identify active services and their versions, and Wireshark analyzes traffic to uncover unencrypted transmissions. A mix of automated scans and manual analysis by experts is crucial here, as machines often cannot fully grasp the business context.
After these tests, the Public Key Infrastructure (PKI) is specifically reviewed to validate certificates and protocols.
Validation of the Public Key Infrastructure (PKI)
Auditors check certificates, modern protocols such as TLS 1.3, strong algorithms like AES-256, and the configuration of Hardware Security Modules (HSMs). These modules ensure secure key storage and enable precise access logs.
Control of Key Rotation
The regular rotation of keys is crucial to prevent unauthorized access. Auditors analyze samples and review rotation and deletion logs to ensure that keys are exchanged correctly. Additionally, so-called fire drill simulations are conducted to test the procedures for compromised or expired keys. These regular checks are a central part of the security concept at Gunfinder.
Addressing Security Issues Through Audits
Identifying security gaps is only the first step. Audits provide not only an analysis but also clear measures to address these vulnerabilities. Once problems are identified, the proposed steps ensure that security gaps are effectively closed. Here you will learn what measures audits recommend to improve encryption security in the long term.
Establishment of an Independent Key Management
A central component of the security strategy is a clearly defined process for the entire lifecycle of keys. This begins with generation using high-quality random number generators, includes secure storage, regular rotation, and ends with final destruction [17][6]. A common criticism in audits is the blind trust in cloud default settings. The solution? The use of Hardware Security Modules (HSMs) or specialized software for internal key control [17][8].
The principle of separation of duties plays a crucial role here. No single employee should be responsible for the entire lifecycle of a key. Multi-level approvals for key generation and destruction are therefore essential [8]. Instead of storing keys in tables, companies should switch to centralized platforms or cryptographic vaults to avoid losses and unauthorized access [6]. Mark Sharron from ISMS.online puts it aptly:
“A clear cryptography policy transforms hidden stress into measurable trust" [8].
Audits also recommend creating a complete inventory of all encrypted assets – from backups to cloud instances to mobile devices. This ensures that no "shadow IT" exists without encryption [8]. A solid key management lays the foundation for further optimizations.
Confirmation of strong encryption methods
Audits check whether modern algorithms such as AES-256 and TLS 1.3 are used and document their correct implementation. Each key should have a defined validity period to ensure regular rotations. This minimizes potential damage in the event of a compromise [6].
Another focus is on integration into zero-trust security models. Encryption must be consistently implemented in hybrid environments – at rest, in transit, and in use [8]. A traceability matrix connects each policy requirement with a technical control and a documented audit artifact [8]. As ecos.de puts it:
“Encryption is only as strong as the process used to manage the corresponding keys" [17].
These audits create the foundation for the use of modern automation solutions.
Use of automation tools
Modern audits place great emphasis on automation to make the creation, renewal, and revocation of certificates and keys more efficient. Tools like the ECOS Trust Management Appliance (TMA) offer automated Certificate Lifecycle Management (CLM). This helps manage the growing number of certificates and prevent outages due to expired certificates [6].
Computer-Assisted Audit Techniques (CAATs) make it easier for auditors to analyze large amounts of data faster than with manual methods [11]. Artificial intelligence increases the detection accuracy of security issues from 70–80% to an impressive 90–95% [11]. Additionally, automated patch management systems immediately close vulnerabilities in outdated software – one of the most common attack vectors [18].
For you as a Gunfinder user, this means: Automated solutions for key rotation, certificate management, and continuous monitoring enhance security while significantly reducing manual effort.
How Gunfinder benefits from encryption audits
Encryption audits play a crucial role in the security of Gunfinder, an online marketplace for hunters and sport shooters. The platform processes sensitive information daily, such as identity proofs and payment data. Audits ensure that this data is protected both at rest and during transmission [19][4].
A major advantage lies in the compliance with GDPR requirements, particularly Article 32, which calls for the implementation of appropriate technical and organizational measures [15][16]. Audits document the implementation of these measures, thereby creating transparency. Globeria Datenschutz aptly describes the added value of such measures:
“A data protection audit... not only creates legal certainty but also strengthens the trust of customers, partners, and employees" [15].
In addition, audits are essential for securing payment processes. In addition to the GDPR, standards such as the Payment Card Industry Data Security Standard (PCI DSS) play an important role here. Audits check whether protective measures such as Multi-Factor Authentication (MFA) and role-based access controls are implemented correctly [11][20]. Additionally, technical tests such as penetration tests uncover vulnerabilities in APIs, firewalls, or outdated software before they can be exploited [11][13]. Given that 19% of all data breaches are caused by vulnerabilities in third-party providers, reviewing external payment service providers is particularly important. Such breaches cost an average of 4.67 million euros [20].
With investments between 5,000 and 25,000 euros, Gunfinder ensures that transactions run smoothly and potentially costly data breaches are avoided – the global average cost of a data breach is 4.45 million US dollars [16][4]. For you as a user, this means: Your data is protected by multiple verified security measures, and the platform meets all legal requirements for the safe trade of weapons and accessories.
Conclusion
Audits are a systematic means of uncovering and addressing vulnerabilities in encryption before attackers can exploit them. They reveal specific technical issues, such as outdated algorithms, insecure key management, or faulty configurations, and provide a clear plan for prioritizing the necessary actions [11][3].
Furthermore, audits implement security policies in practice and address risks such as unsecured shadow IT [11][12]. The result? Improved technical security and assurance of compliance with legal regulations.
For standards such as GDPR, ISO 27001, and PCI DSS, audits are indispensable. They document compliance and minimize the risk of high fines – up to 20 million euros or 4% of global annual revenue [20]. Given the average cost of $4.45 million per data breach, audits are a worthwhile measure [4].
The trend is shifting from occasional reviews to continuous monitoring and AI-driven systems that can detect threats almost in real-time – instead of only after weeks or months [11][13]. For Gunfinder, this means staying up to date with security. And for you as a user: a higher level of security and increased trust in the protection of your data.
FAQs
How often should an encryption audit take place?
An encryption audit should ideally take place at least once a year. Additionally, it is advisable to conduct such audits when there are changes in processes or a new management system is implemented. Especially in such situations, event-driven audits can help identify potential security gaps early and effectively close them.
What should be prepared internally before an audit?
Thorough preparation is key to a smooth audit. Review the security infrastructure, existing processes, and documentation to ensure everything is up to date.
It is important that all relevant data, access, and documents are available in a timely manner. A checklist can help systematically address all important points.
This thorough preparation not only makes it easier to manage the audit process but also helps to identify potential weaknesses early on.
How do I know if your key management is really secure?
Regular audits play a central role in ensuring the security of your key management. They allow for the early detection and correction of potential vulnerabilities or misconfigurations.
The advantage? You minimize the risk of unauthorized access and ensure that your encryption systems continue to operate effectively. An audit is thus not only a security measure but also an important step in protecting the integrity of your data in the long term.